Namespaces
Nomad has support for namespaces, which allow jobs and their associated objects to be segmented from each other and other users of the cluster.
Nomad places all jobs and their derived objects into namespaces. These include jobs, allocations, deployments, and evaluations.
Nomad does not namespace objects that are shared across multiple namespaces. This includes nodes, ACL policies, Sentinel policies, and quota specifications.
In this guide, you'll create and manage a namespace with the CLI. After creating the namespace, you then learn how to deploy and manage a job within that namespace. Finally, you practice securing the namespace.
Create and view a namespace
You can manage namespaces with the nomad namespace subcommand.
Create the namespace of a cluster.
List the namespaces of a cluster.
Run a job in a namespace
To run a job in a specific namespace, annotate the job with the namespace
parameter. If omitted, the job will be run in the default namespace. Below is
an example of running the job in the newly created web-qa namespace:
Use namespaces in the CLI and UI
Nomad CLI
When using commands that operate on objects that are namespaced, the namespace
can be specified either with the flag -namespace or read from the
NOMAD_NAMESPACE environment variable.
Request job status using the -namespace flag.
Export the NOMAD_NAMESPACE environment variable.
Use the exported environment variable to request job status.
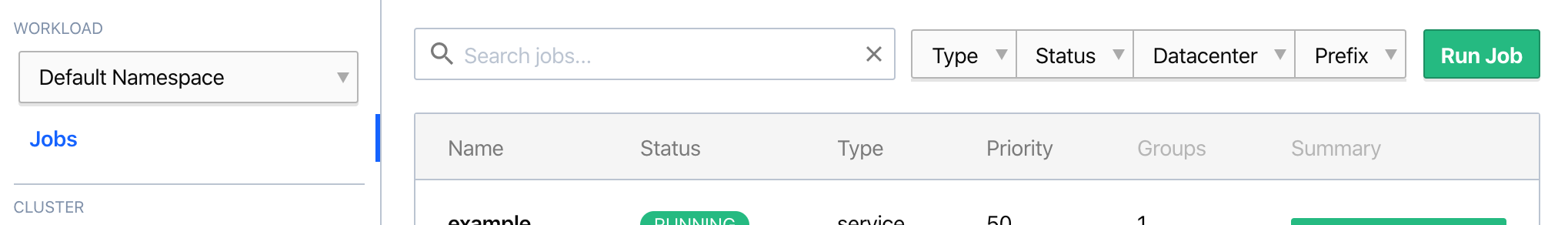
Nomad UI
The Nomad UI provides a drop-down menu to allow operators to select the namespace that they would like to control. The drop-down will appear once there are namespaces defined. It is located in the top section of the left-hand column of the interface under the "WORKLOAD" label.
Secure a namespace
Access to namespaces can be restricted using ACLs. As an example, you could create an ACL policy that allows full access to the QA environment for the web namespaces but restrict the production access by creating the following policy:
Learn more about namespaces
For specific details about working with namespaces, consult the namespace commands and HTTP API documentation.